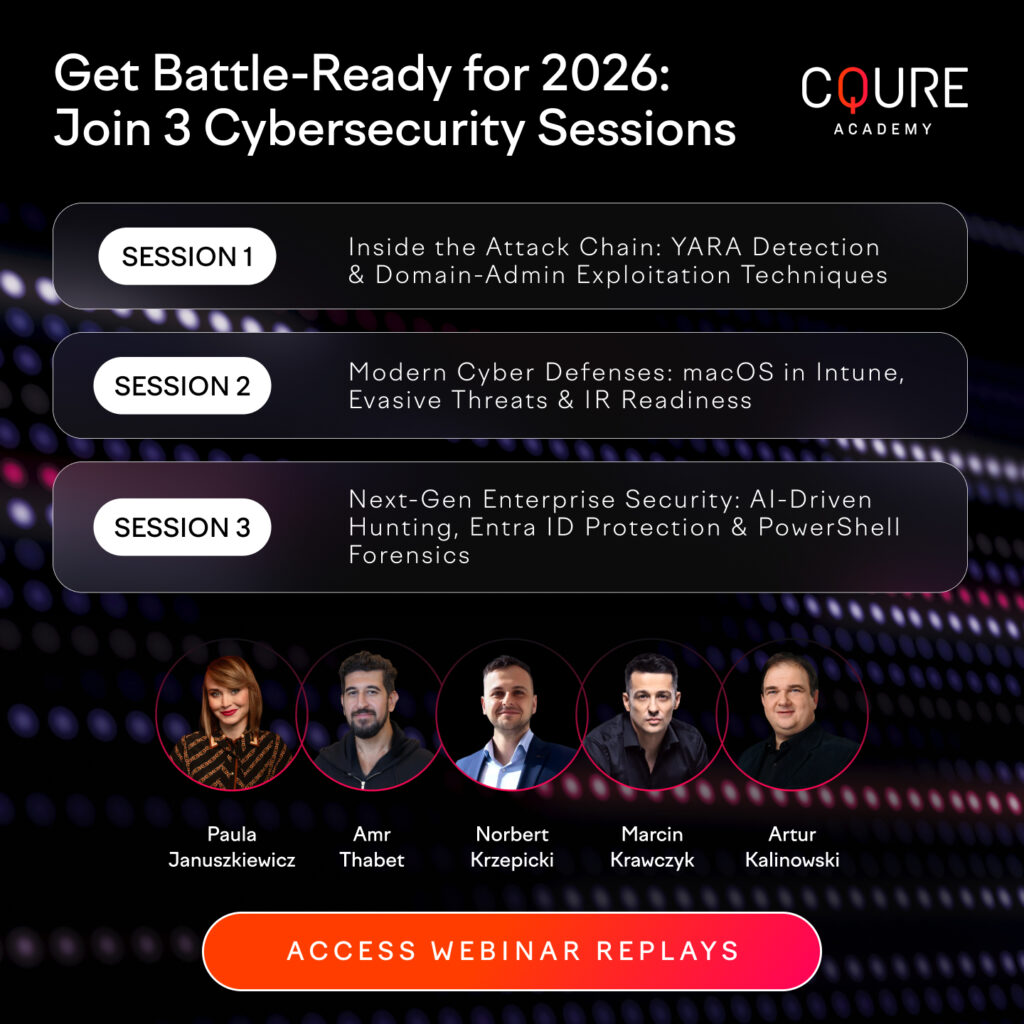
What our students say:
I have attended CQURE’s training as someone who is not a security professional, but just an enthusiast, and I feel like I learned a A LOT. The whole training was loaded with information and nice demos of the latest technologies. On top of that — having an opportunity to ask and talk to professionals was priceless.

Marek Chmel
SQL Server DBA | AT&T