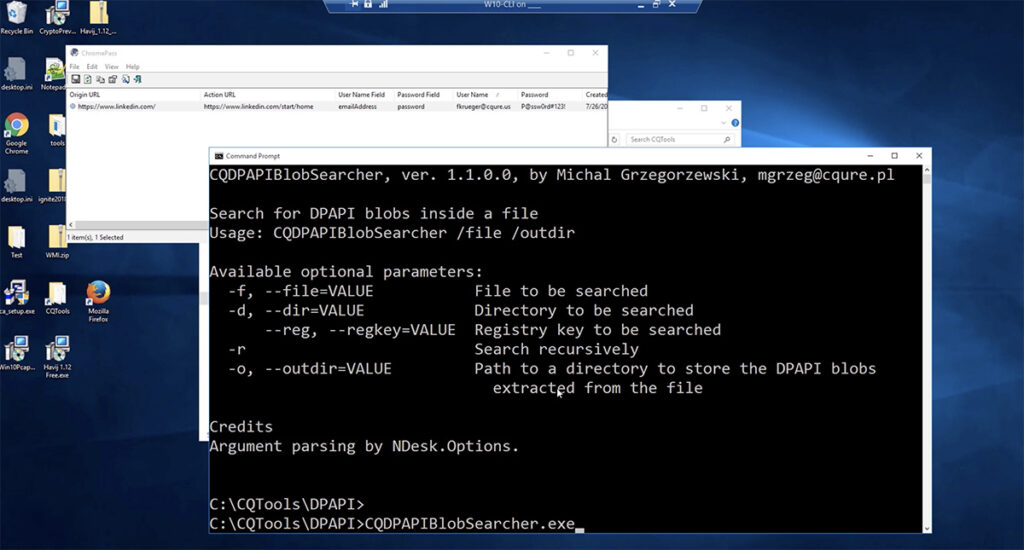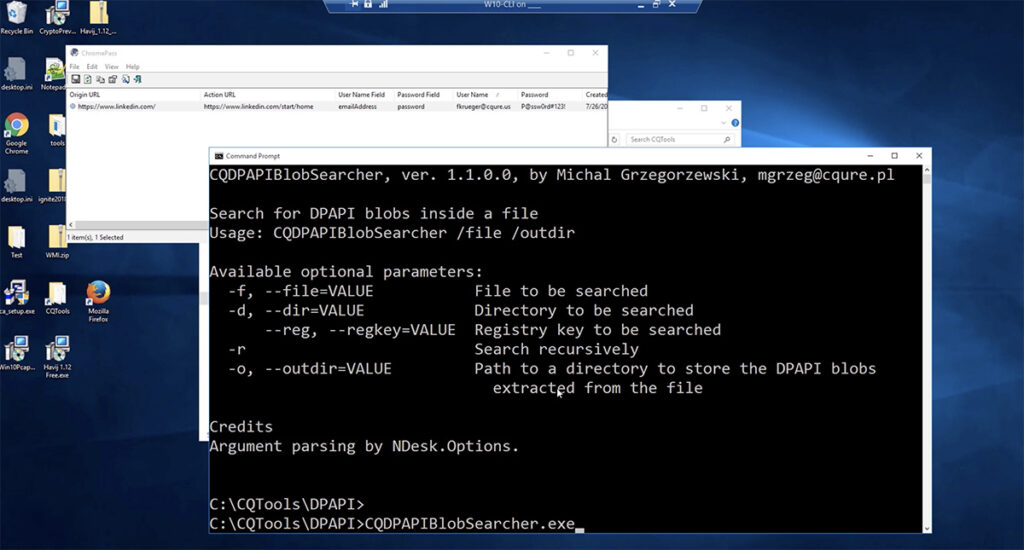
What is DPAPI? Data Protection Application Programming Interface (DPAPI) is used in many Windows applications and subsystems. What is its purpose? For example: Credentials of Microsoft Outlook accounts stored in the registry; Credentials and encrypted cookies stored by Google Chrome; Credentials stored by IE in the registry under HKCU\Software\Microsoft\Internet Explorer; WiFi passwords saved in XML […]
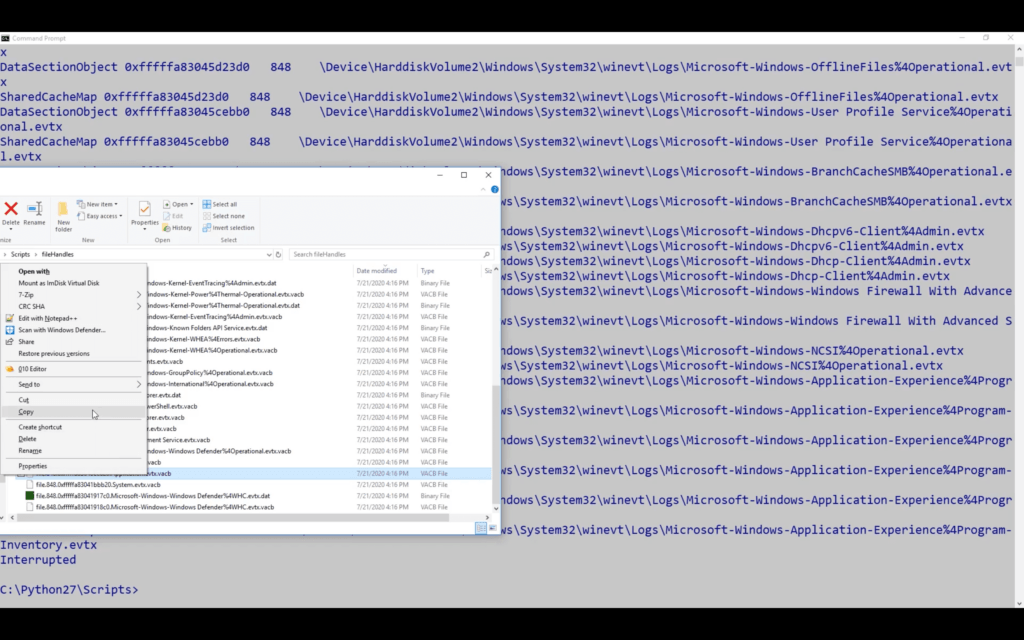
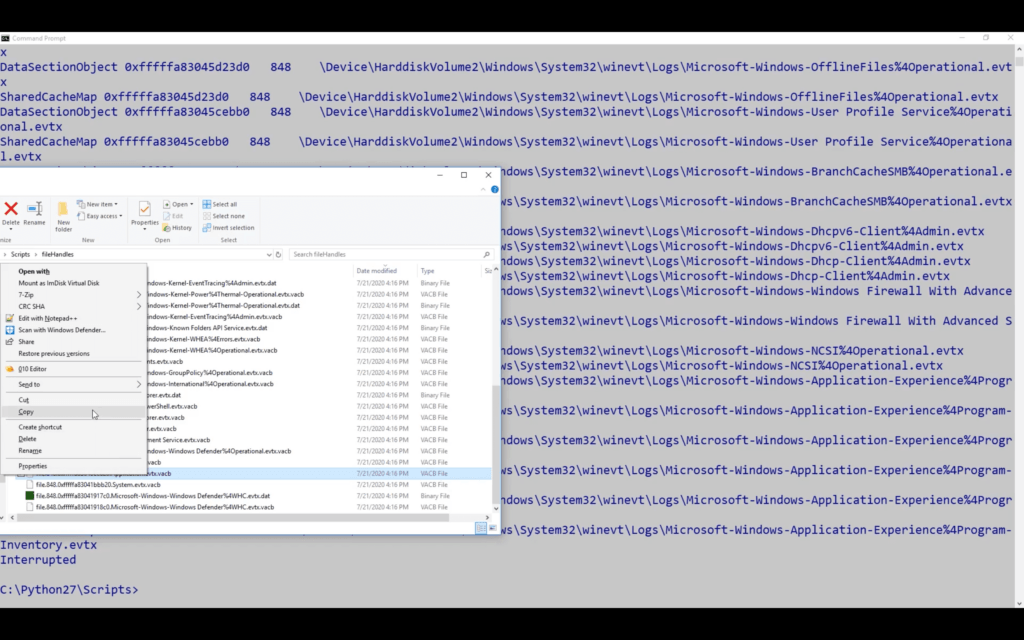
Find out: how to recover corrupted EVTX log files recover log files directly from a memory dump Watch the full video for more details and examples. Tools for EVTX file recovery Our experts developed this particular tool because there are so few options available online for fixing EVTX files. Try our CQEVTXRecovery tool. It is […]
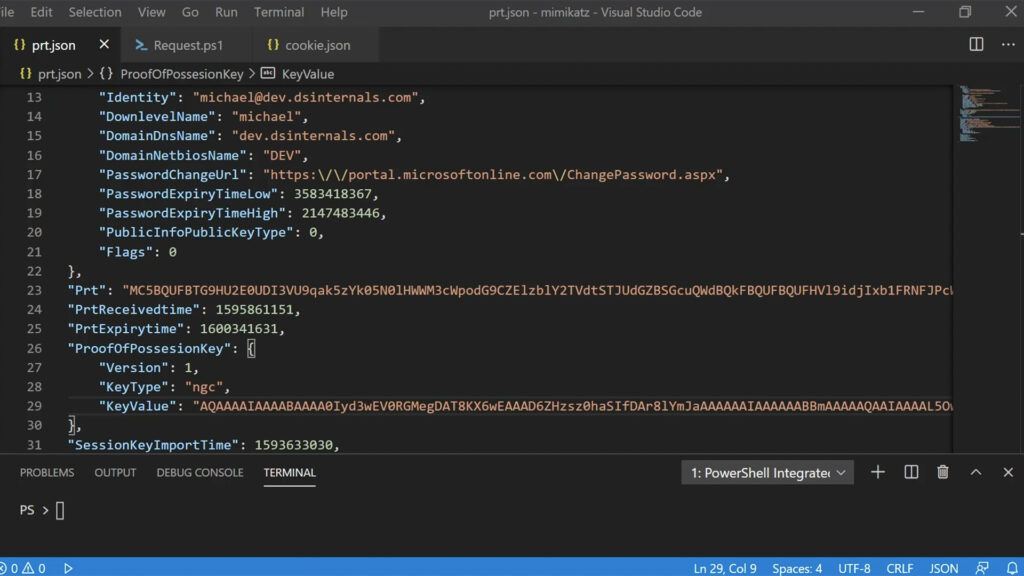
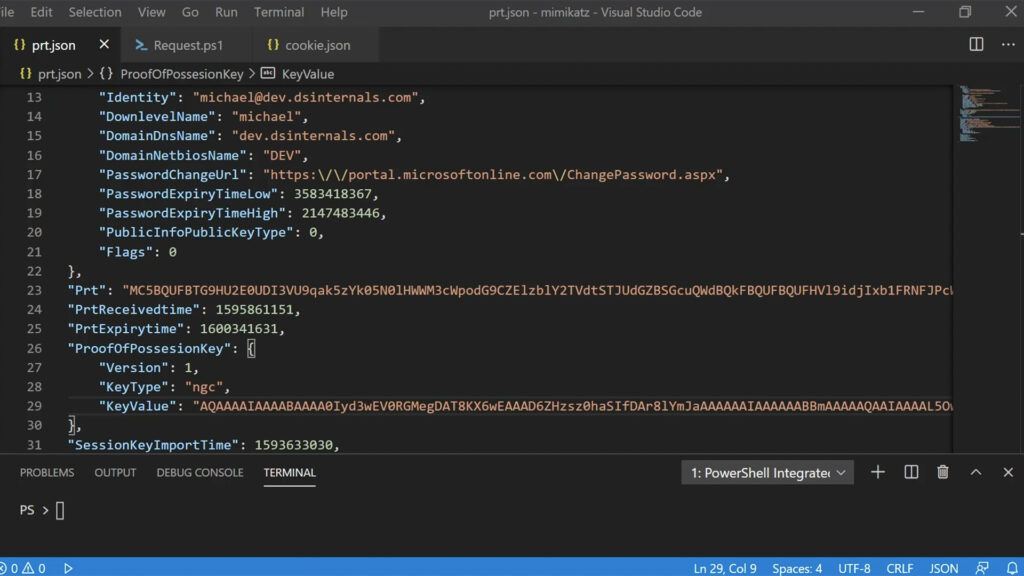
Discover what a Primary Refresh Token is and how cyber-criminals are exploiting it in two different ways to launch Azure Active Directory attacks.

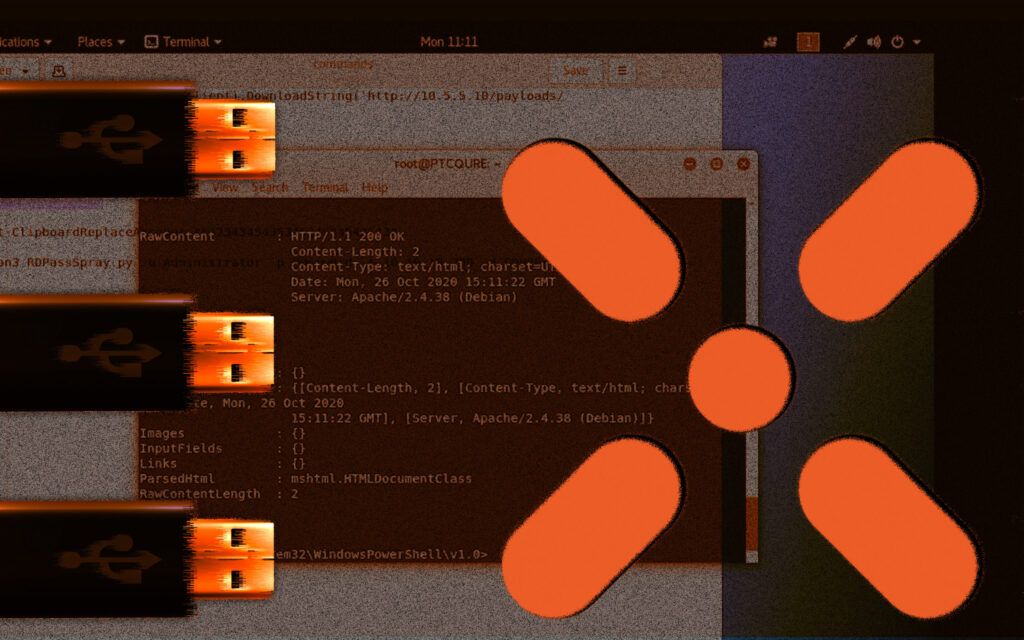
Find out how Paula J, CQURE Academy CEO performs Man-in-the-middle attack, to know what to be aware of.
Find out how Paula J, CQURE Academy CEO performs Man-in-the-middle attack, to know what to be aware of.
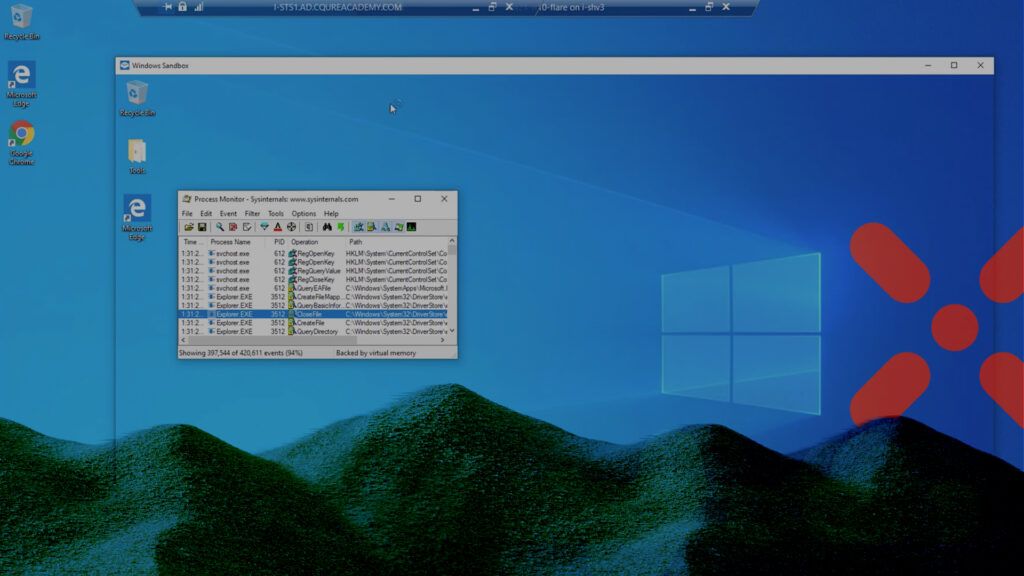
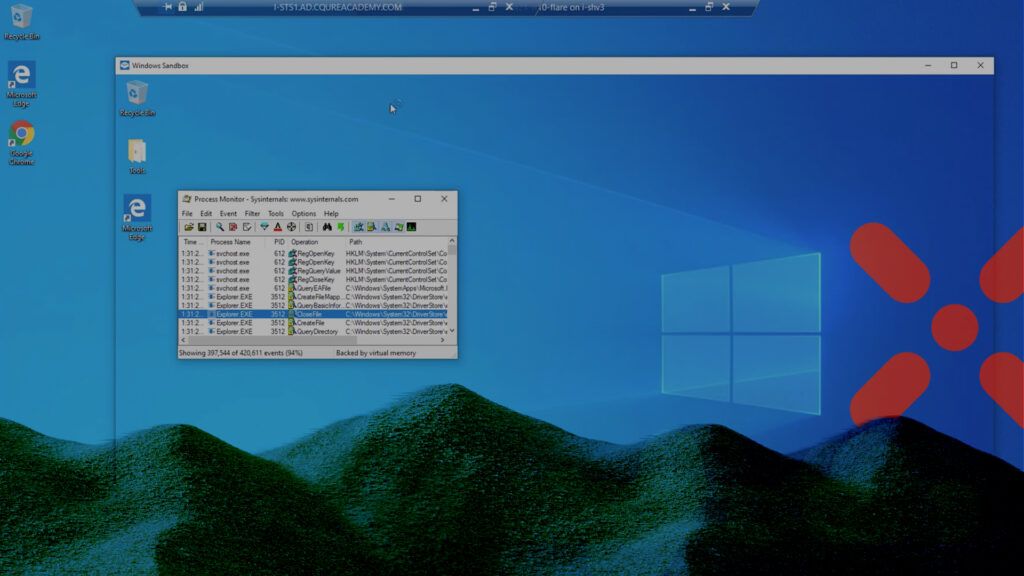
Windows Sandbox can protect your PC from malicious executables. Here’s how to install and configure it correctly from a security expert.