Welcome to another episode of CQURE Hacks Weekly. This time we’re going to discuss how to perform a memory dump. It is a very useful process, sometimes even a crucial one. Don’t forget about memory dump in case of any security incident when you need to collect the evidence and understand what happened.
Memory dump in general is useful in order to investigate what’s running in our system memory. Everything, all information that was running before the crash is stored in our memory.
For example, if there is any kind of malicious code that is running in the memory of a legitimate process, then you would be able to extract information and find that piece of code. Of course – when the memory dump was collected. We all know that a memory dump as well as a memory itself is volatile.
Therefore, in order to perform the memory dump, you need to be sure that everything works smoothly. You need to have good tools prepared in advance. You need to know all the conditions met to be successful during the process. Actually, sometimes you can experience a blue screen.
While we are doing a memory dump, there are a bunch of good techniques that you can apply.
It’s absolutely interesting but not all of the memory acquisition tools can actually complete the memory dump while a VSM (Virtual Secure Mode) is enabled. But of course, whenever we are thinking about some successful dumping tools here, we should test the Belkasoft RAM Capturer and also DumpIt. But for now, we were using the FTK imager at the moment the video is recorded, and we were getting blue screens.
And VSM, of course, it’s not really the only reason why you can experience the blue screen, and that is simply coming from the fact how the drivers that are used within the memory dumping tools are written. And that could be even a case of an accident that the blue screen is going to happen. So that’s something that you can always expect.
But in order to minimize the risk, you need to use a tool tested by yourself.
In order to be an efficient person who does the memory dump quickly and well, you need to make sure that you are staying up to date with all the tools working in given conditions. So this is just to give you a heads up that for the time we are recording this video, you are able to successfully perform the memory dump with the DumpIt tool which is written by Matthew Suiche.
So let me, of course, start the demonstration. Let’s dig in.
So what you see on the screen right now, it’s just simply a console running with an administrator, with administrator’s privileges. We’re going to launch DumpIt, which is an amazing tool that is very respected worldwide and used by us for years, written by Matthew Suiche.
And within this tool, we are performing the memory dump on the external and to the external drive.
So we run DumpIt from the external disk and we are dumping, of course, the output to the external disk.
It takes a while, but here we just run the command DumpIt /O, and then we specify the name of a file.
Of course, the name of a file here on the video is Windows 10 Evidence.
But it’s a good practice to use not only the Windows version but also a date and time proper for a moment of performing the memory dump.
When you’re going to have multiple file dumps to analyze, it will be great not only to differentiate by time but also to differentiate by version. Thanks to that you can use the appropriate volatility module and analyze that memory dump to be just simply more efficient and faster in terms of extracting information from the dump itself.
And well, yes, you need to always wait for a second, we are keeping it realistic over here and for that reason, you can see that the processing part, it just simply takes a while.
And this is the moment where all of the memory is being stored to the disk.
We should always remember about the good practice, let me mention that too as well – we always keep and do the memory dump first and then we do the disk dump as second.
And that is not really the best practice over there, but I would say a necessity. This is something that simply affects the operations when you perform the memory dump, and that could be also recorded on the disk.
For example, any kind of activity could impact as well the USN Journal but one of the most important things here is to notice that, as I mentioned earlier, memory is volatile, which means that the faster we perform the memory dump, the better.
And that’s always one of the requirements over here.
And also when we look into some other good practices here. What is important is that whenever we are thinking about different tools and different devices – all must be tested in advance.
What is important is that the suspect’s device, so the computer and so on, should never be used, should never be touched to store any kind of captured information and data. This information must be always stored on the external storage devices. What is important is that this will give us always a context of what at that certain moment happened in the attack, hopefully.
So over here you can see that we just finished the dump and that took us a certain time.
Here we’ve got also the SHA–256 calculated.
There’s also the path to JSON and this is something that we need to store as well.
So regarding this, when we will be going to analyze that particular dump, we need to make sure that this hasn’t been touched and also it’s super important to do a copy of it.
Let’s just demonstrate it.
We are doing the copy of the dump and then of course we keep the original dump somewhere out there in a safe location.
And over here we can also use the certutil hashfile.
And then we’ve got a Windows 10 analysis dump, and then we’ve got our SHA-256 that we are calculating. Once again, of course, the algorithm here is the one of your choices, depending on a project, but this one, in this case, is a good choice.
We can do the echo and also store it as hash2 for a reference to support the other file.
And then we can do the file comparison.
And as you can see, these two files are simply the same and we can start the next analysis from this point.
Hopefully, this was interesting for you and pretty straightforward, as DumpIt works very smoothly.
It’s important to know all the background and the real need of using reliable, good tools. It is really the worst thing that we can encounter here, it’s a blue screen during the memory dumping operation.
So hopefully that was useful.
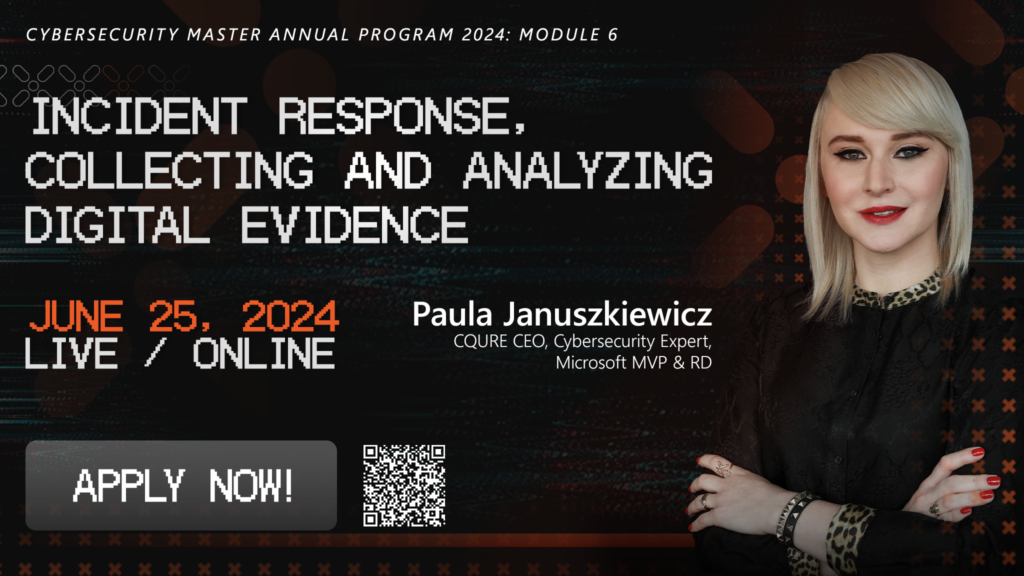
💡 If you would like to further your knowledge in evidence gathering make sure to check Collecting and Analyzing Digital Evidence!
Please let us know if you have any questions and we absolutely hope to see you in further episodes of the CQURE Hacks Weekly.


Do you want to receive the geekiest cybersecurity solutions, tools, and tricks, straight to your inbox?
Learn more about our offer in terms of Consulting. Our Cybersecurity Experts perform consulting work on a daily basis, hence we are fully prepared for any challenge.
Learn more about our offer in terms of Consulting. Our Cybersecurity Experts perform consulting work on a daily basis, hence we are fully prepared for any challenge.
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.